From Raw logs to actionable intelligence — in seconds.
SieMMax ingests events from every source in your environment — servers, endpoints, PLCs, cloud APIs, CCTV — and classifies threats using MITRE ATT&CK® aligned models. Not rules. Not regex. Reasoning.
- MITRE ATT&CK® mapped detection
- Correlation engine processes
- Behavioural baselining per asset, per user
- AI suggested severity with full rationale — no black box scoring
- Triple whitelist matching: source IP + user account + target asset
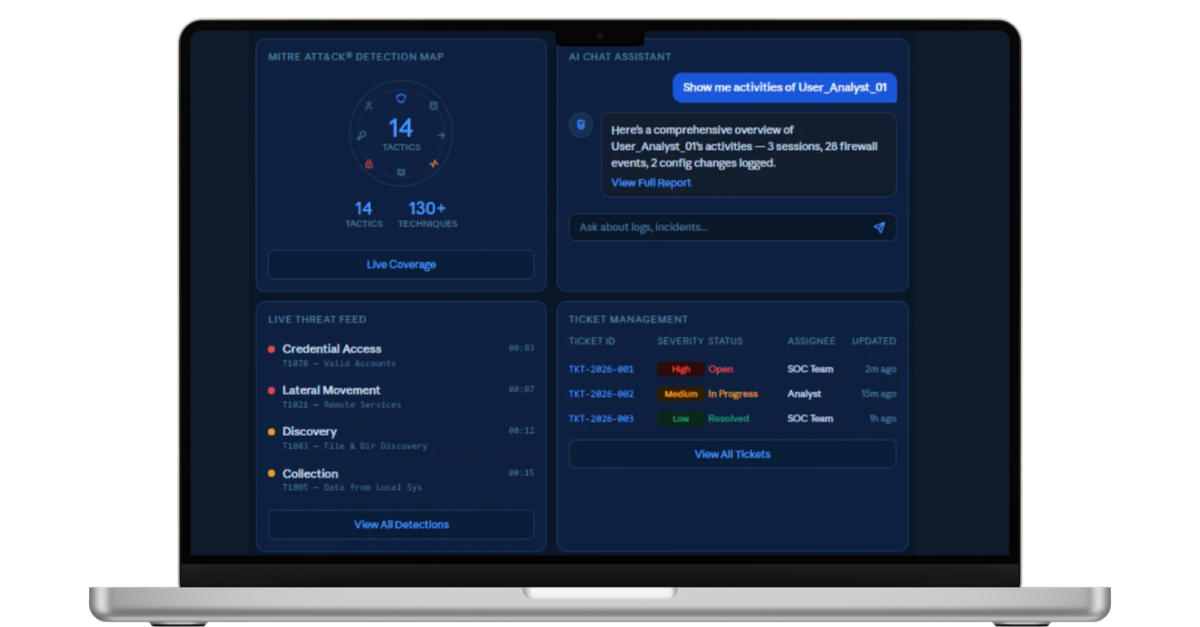
Automated L1, human-guided L2/L3 — without hiring a SOC team.
SieMMax runs core SOC operations autonomously. L1 triage, noise reduction, and pre-approved responses happen automatically. L2/L3 analysis is AI-assisted — humans stay in command of every decision that matters.
- AI classifies and prioritises alerts using playbooks and context
- Email, Teams, Slack, and interactive voice call notifications
- Pre-approved SOAR actions — block IP, disable user, isolate endpoint
- Agentic AI for L2/L3 investigation, forensic summaries, and narratives
- Pending SOAR workflows held for human approval before execution
- Incidents identified, escalated, and tracked automatically

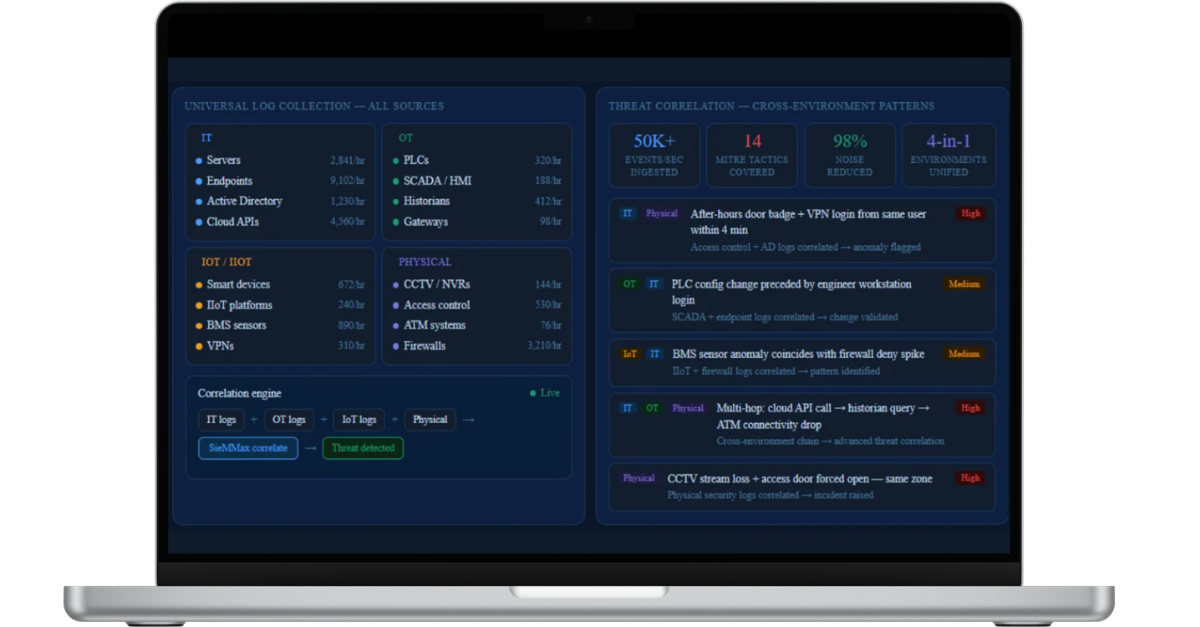
Universal log collection and threat correlation — across every environment.
Collect logs from across your infrastructure — servers, endpoints, IoT, OT, VPNs, firewalls, and cloud — then correlate them to identify patterns, anomalies, and advanced threats.
- IT: Servers, endpoints, Active Directory, cloud platforms, VPNs
- OT & Industrial: PLCs, SCADA, gateways, historians, HMI
- IoT / IIoT: BMS, smart devices, industrial sensors, IIoT platforms
- Physical: CCTV, NVRs, access control, ATM logs, firewalls
- Cross-environment correlation — detect multi-hop attack chains
If it produces logs, SieMMax can monitor it
The visibility regulators expect — without the enterprise overhead
SieMMax gives regulated organisations the centralised logging, access controls, and incident records they need to demonstrate security readiness — with complete timelines, evidence trails, and AI-drafted reports.
- Centralised log collection, retention, and tamper-evident audit trails
- RBAC, MFA, and detailed access logs across all users
- On-premises deployment for regulated and air-gapped environments
- Full incident timelines — evidence, annotations, escalation, ownership
- AI-drafted weekly and monthly SOC reports for leadership
- Deterministic, rule-based workflows — no opaque AI decisions

Defend against the attacks of today — including AI-generated ones.
SieMMax validates indicators of compromise, correlates multi-stage attack patterns, and continuously improves detection as your environment evolves — so your defences get sharper over time, automatically.
- IOC validation against available threat intelligence sources
- Deep web exposure checks via free-tier intelligence feeds
- RFC1918 private IP recognition — no false enrichment
- Cross-alert MITRE ATT&CK® tactic and technique mapping per incident
- Threat intel feed with reputation, domain age, and flag scoring
- AI Max continuously tunes rules and playbooks based on outcomes

