Live — AI Max Now Available
The SIEM That Operates Your SOC Automatically.
Stop hiring for 24/7 shifts. SieMMax combines enterprise-grade SIEM with AI-driven SOC automation to monitor IT, OT, and IoT environments in real-time.

The Problem
Why Most SIEM Deployments Fall Short
0%
Of alerts never reach investigation
The Noise Floor
Too many alerts, not enough action. Analysts spend more time filtering than responding
0X
Cost Growth - As log volume increases
The Pricing Problem
High costs driven by log volume and EPS-based licensing make scaling difficult.
0%
Of OT assets remain unmonitored
The OT Blindspot
Most SIEMs lack deep visibility into industrial systems, CCTV, and connected infrastructure.
0×7
Dependency - For effective monitoring
The SOC Staffing Trap
Requires round-the-clock SOC staffing just to maintain visibility and response readiness.
Cloud-Only Limits
For regulated industries
The Deployment Constraint
Cloud-only SIEM models often fail compliance, sovereignty, and on-premise security requirements.
Slow Investigation Cycles
Due to fragmented telemetry
The Visibility Fragmentation
Disconnected tools and siloed logs slow investigations and reduce operational efficiency.
Core platform
Five capabilities. One platform.
SieMMax is not a tool. It is an operating layer for your entire security posture.
AI-Powered Detection
Autonomous SOC
Universal Log Collection
Security & Audit Trails
Threat Intelligence
From Raw logs to actionable intelligence — in seconds.
SieMMax ingests events from every source in your environment — servers, endpoints, PLCs, cloud APIs, CCTV — and classifies threats using MITRE ATT&CK® aligned models. Not rules. Not regex. Reasoning.
- MITRE ATT&CK® mapped detection
- Correlation engine processes
- Behavioural baselining per asset, per user
- AI suggested severity with full rationale — no black box scoring
- Triple whitelist matching: source IP + user account + target asset
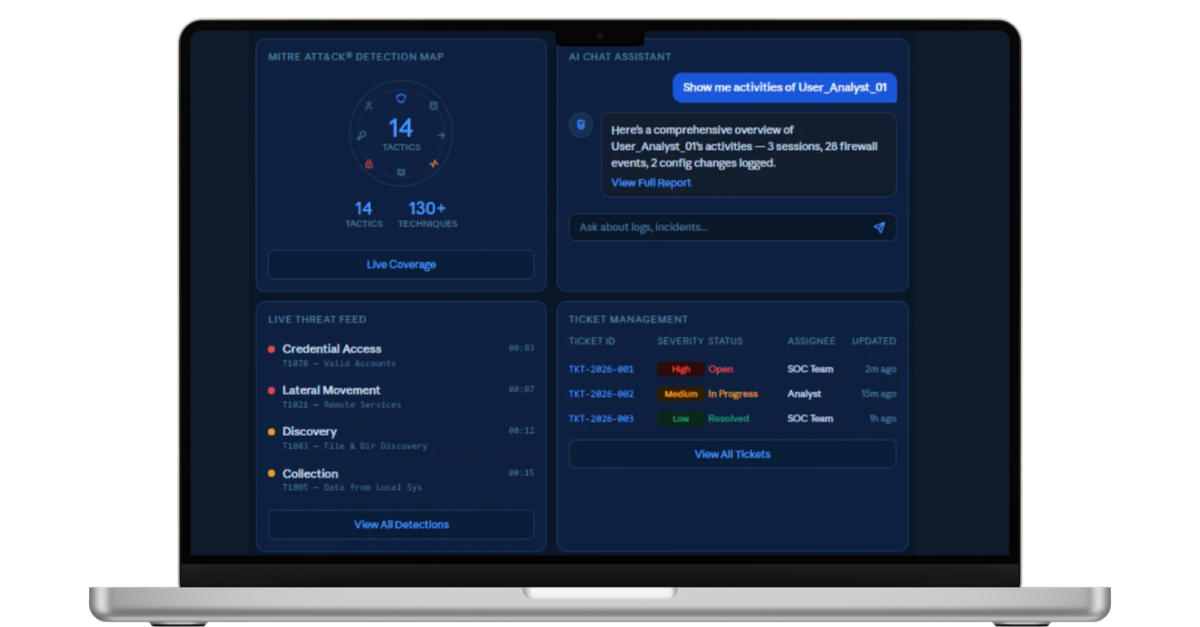
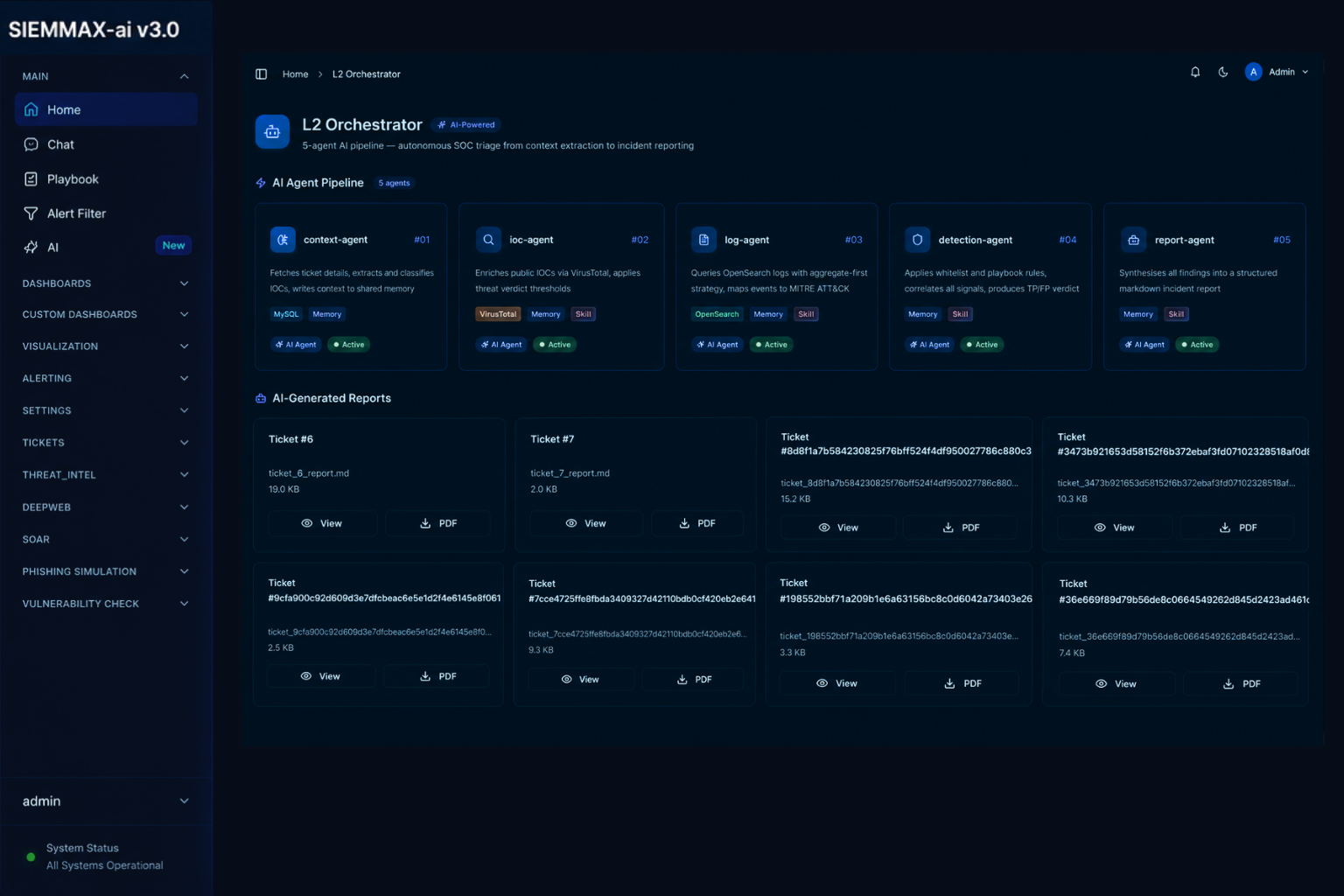
Automated L1, human-guided L2/L3 — without hiring a SOC team.
SieMMax runs core SOC operations autonomously. L1 triage, noise reduction, and pre-approved responses happen automatically. L2/L3 analysis is AI-assisted — humans stay in command of every decision that matters.
- AI classifies and prioritises alerts using playbooks and context
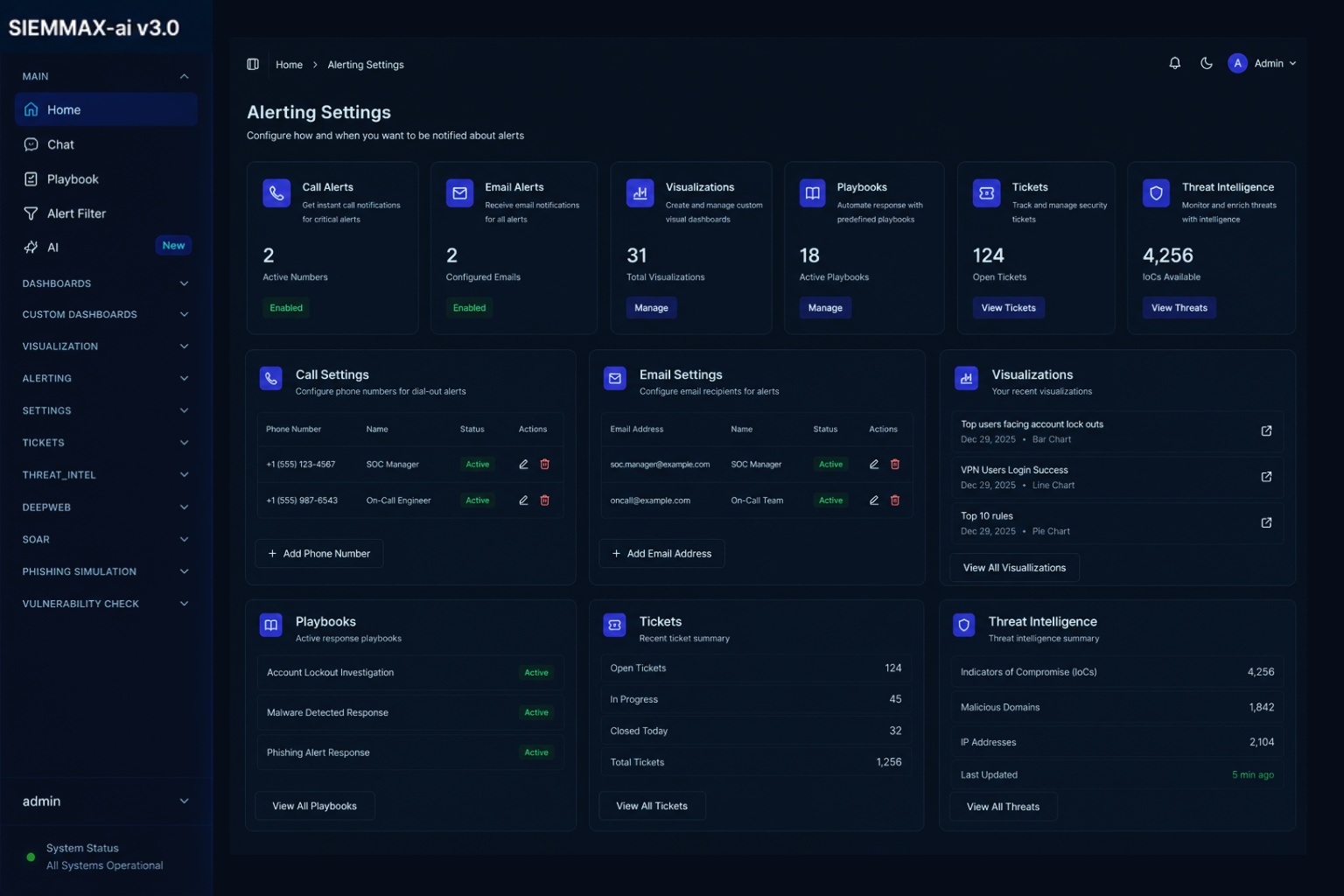
- Email, Teams, Slack, and interactive voice call notifications
- Pre-approved SOAR actions — block IP, disable user, isolate endpoint
- Agentic AI for L2/L3 investigation, forensic summaries, and narratives
- Pending SOAR workflows held for human approval before execution
- Incidents identified, escalated, and tracked automatically

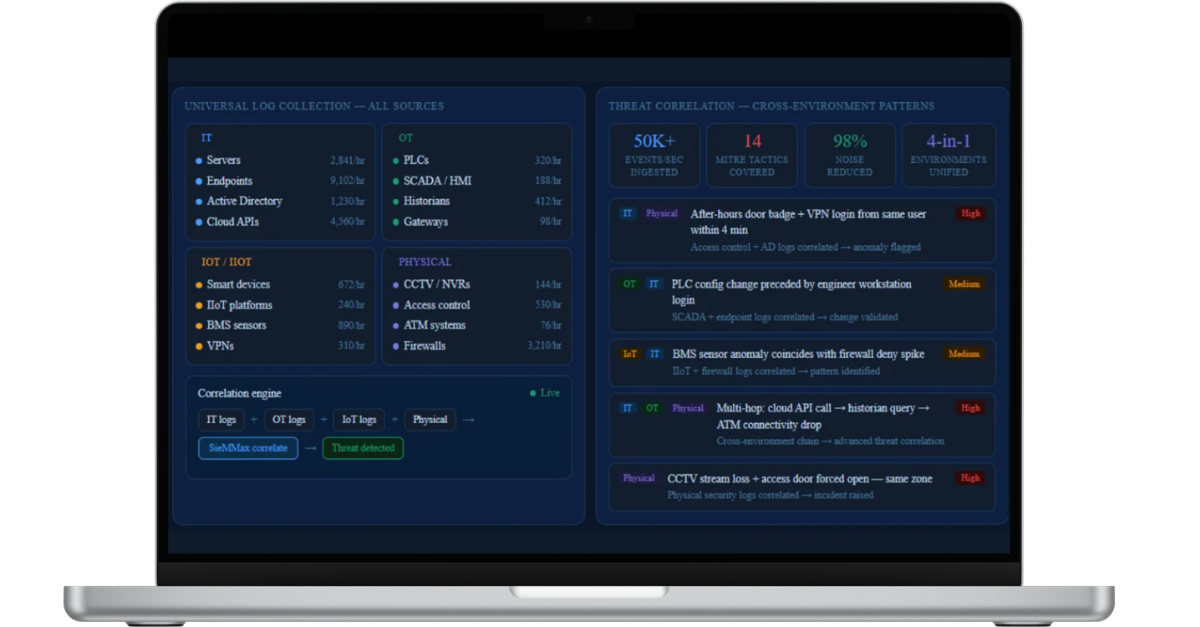
Universal log collection and threat correlation — across every environment.
Collect logs from across your infrastructure — servers, endpoints, IoT, OT, VPNs, firewalls, and cloud — then correlate them to identify patterns, anomalies, and advanced threats.
- IT: Servers, endpoints, Active Directory, cloud platforms, VPNs
- OT & Industrial: PLCs, SCADA, gateways, historians, HMI
- IoT / IIoT: BMS, smart devices, industrial sensors, IIoT platforms
- Physical: CCTV, NVRs, access control, ATM logs, firewalls
- Cross-environment correlation — detect multi-hop attack chains
If it produces logs, SieMMax can monitor it
The visibility regulators expect — without the enterprise overhead
SieMMax gives regulated organisations the centralised logging, access controls, and incident records they need to demonstrate security readiness — with complete timelines, evidence trails, and AI-drafted reports.
- Centralised log collection, retention, and tamper-evident audit trails
- RBAC, MFA, and detailed access logs across all users
- On-premises deployment for regulated and air-gapped environments
- Full incident timelines — evidence, annotations, escalation, ownership
- AI-drafted weekly and monthly SOC reports for leadership
- Deterministic, rule-based workflows — no opaque AI decisions

Defend against the attacks of today — including AI-generated ones.
SieMMax validates indicators of compromise, correlates multi-stage attack patterns, and continuously improves detection as your environment evolves — so your defences get sharper over time, automatically.
- IOC validation against available threat intelligence sources
- Deep web exposure checks via free-tier intelligence feeds
- RFC1918 private IP recognition — no false enrichment
- Cross-alert MITRE ATT&CK® tactic and technique mapping per incident
- Threat intel feed with reputation, domain age, and flag scoring
- AI Max continuously tunes rules and playbooks based on outcomes

How It Works
Three steps from deployment to defended.
Connect Everything
Let the AI Reason
Respond Before Impact
Pricing
Choose your level of Automation.
Start where you are. Scale as your threat landscape grows.
Starter
SieMMax Essential
Foundational SIEM with rule-based detection, dashboards, and email alerting
- SieMMax console
- Agent, API & Syslog integration
- Decoders, Rules & MITRE Framework
- Threat Intel (IP, Hash, Email Domain)
- In-Built Critical Alerts & Email alerting
- Cloud + On-Prem deployment
- 12×5 Email Support, 1 Health Check/yr
AI Pro
SieMMax AI Pro
SIEM + SOAR + AI assistance for teams who need response automation.
- Everything in Essential
- Deepweb Search & Threat Intel
- AI Call Alert - limited minutes/month
- SOAR workflows + Auto alert mitigation
- L1 AI Incident Analysis
- Chat Bot - limited prompts/month
- 24×7 Email Support, 2 Health Checks/yr
Advanced
SieMMax AI Max
The complete AI-native SOC- full coverage, deeper analysis, premium support
- Everything in AI Pro
- Agentic AI for L2/L3 analysis
- Vulnerability Scanner (OpenVAS) included
- UEBA Analytics built-in
- AI Call Alert - Extra minutes/month
- Chat Bot — More prompts/month
- 24×7 Email + Call Support, 4 Health Checks/yr
One SIEM. Many Environments.
Still Using an Overbuilt SIEM — Or None at All?
Environment Coverage
IT Systems
Cloud & SaaS
OT / Industrial
Physical Security
Unified Visibility
SOC Continuity
Email Alerts
24×7 Monitoring
Voice Escalation
Alert Acknowledgement
Shift Coverage
Deployment Flexibility
On-Prem
Air-Gapped
Hybrid
Cloud
Data Residency
Security Operations Platform
Phishing Simulation
SOAR
Vulnerability Assessment
Deep-Web Monitoring
Database Monitoring

Unified
Compliance Ready
Response
Continuity
Visibility
Control

Unified
Compliance Ready
Response
Continuity
Visibility
Control

Unified
Compliance Ready
Response
Continuity
Visibility
Control

Unified
Compliance Ready
Response
Continuity
Visibility
Control

Unified
Compliance Ready
Response
Continuity
Visibility
Control

Unified
Compliance Ready
Response
Continuity
Visibility
Control
Why SieMMax
Not just a better SIEM. A different category.
| Capability | SieMMax | Splunk ES | IBM QRadar |
|---|---|---|---|
| IT + OT + IoT monitoring | ✓ | — | — |
| AI-autonomous L2/L3 SOC | ✓ | — | — |
| Interactive Voice Escalation | ✓ | — | — |
| On-prem + air-gapped deployment | ✓ | ✓ | ✓ |
| Built-in vulnerability assessment | ✓ | — | — |
| Dark web credential monitoring | ✓ | — | — |
| Pricing: SMB-accessible | ✓ | — | — |
| Setup time < 24 hours | ✓ | — | — |
Frequently Asked Questions
Yes. It is designed to work across IT, OT, IoT, and hybrid environments, supporting diverse log sources.
No. SieMMax uses practical AI with human control. Actions are only executed when configured, ensuring full transparency and no black-box automation.
No. It is built for lean security and IT teams, making day-to-day operations simple and manageable.
No. SieMMax is designed so you don’t need to build a large SOC team. Core monitoring, triage, and response are automated, especially in AI Pro and Pro Max.
Security Intelligence
Insights from the front line
Threat research, product deep-dives, and security leadership perspectives from the SieMMax team
Get Started
De-risk Your Future. Today.
Whether you need a pure SIEM or an AI-powered SOC layer, SieMMax scales with your risk profile. No consultants. No six-month onboarding. Running in 24 hours




